Introduction
Voice over IP (VoIP) technology has revolutionized communication, offering cost-effective and accessible voice and video calling solutions. However, as digital communication expands, law enforcement agencies, intelligence organizations, and telecom providers face the challenge of intercepting and decoding VoIP traffic while ensuring lawful compliance. This article explores the technical aspects of VoIP media decoding for lawful interception, shedding light on key challenges and methodologies in VoIP media decoding, including VoIP, VoLTE, and VoNR traffic analysis, auto RTP media codec detection, and real-time versus offline packet analysis, helping businesses and agencies enhance their interception capabilities.
What is Lawful Interception in VoIP?
Lawful interception (LI) refers to the legally authorized monitoring of VoIP traffic involving voice, video, fax, and data transmissions across communication networks. Unlike traditional telephone systems, which use circuit-switched networks, VoIP operates over packet-switched networks, making real-time lawful interception significantly more complex. Efficient VoIP decoding solutions are essential for extracting useful intelligence while adhering to privacy regulations.
Key Challenges in Decoding VoIP Media
- Encryption Barriers: Many VoIP services implement Secure Real-time Transport Protocol (SRTP) and Transport Layer Security (TLS), and decryption keys are necessary for decoding.
- Diverse Protocols: VoIP traffic is transmitted using various signaling and media transport protocols, including SIP, H.323, RTP, and WebRTC, requiring adaptable interception techniques.
- Non Availability of SDP metadata: The traffic includes only media (RTP) and absence of SDP information introduces more complexity in media reconstruction.
- Network Performance Issues: Jitter, packet loss and latency can degrade VoIP streams, making media reconstruction challenging.
- NAT and Firewall Restrictions: Network Address Translation (NAT) and firewall settings obscure call participants’ IP addresses, complicating lawful interception efforts.
- VoLTE and VoNR Complexity: Advanced Voice over LTE (VoLTE) and VoNR (5G Voice) networks introduce additional encryption, adaptive bitrate codecs, and complex media transport mechanisms.
- Fax and Real-Time Text Interception: Capturing and decoding T.38 or G711 fax transmissions and RTT data streams requires specialized processing techniques to ensure accurate message reconstruction.
How VoIP Media Decoding Works
1. Packet Capture and Analysis
- Tools like Wireshark, tcpdump, and deep packet inspection (DPI) identify and capture VoIP packets.
- Custom-built solutions optimize VoLTE and VoNR traffic extraction, utilizing IMS (IP Multimedia Subsystem) processing.
- Real-Time and Offline Processing: Support for live RTP stream decoding and offline packet capture (PCAP) file analysis ensures flexibility in intelligence gathering.
2. Reconstructing VoIP Conversations
- Extracting signaling data (SIP, SDP) to identify call participants and media channels. Extraction of this information is not always possible given the architecture of LI systems and hence intelligent algorithms are essential for the auto-detection of RTP media codec detection.
- Reassembling RTP streams for voice, video, fax, and text transmission.
- Decoding VoLTE and VoNR AMR-WB/NB, EVS codecs for high-fidelity speech analysis.
- Auto RTP Media Codec Detection: Intelligent algorithms analyze RTP payloads to detect the correct codec when SDP metadata is unavailable.
- T.38 Fax and RTT Decoding: Specialized software reconstructs T.38 fax images and RTT text messages for forensic analysis.
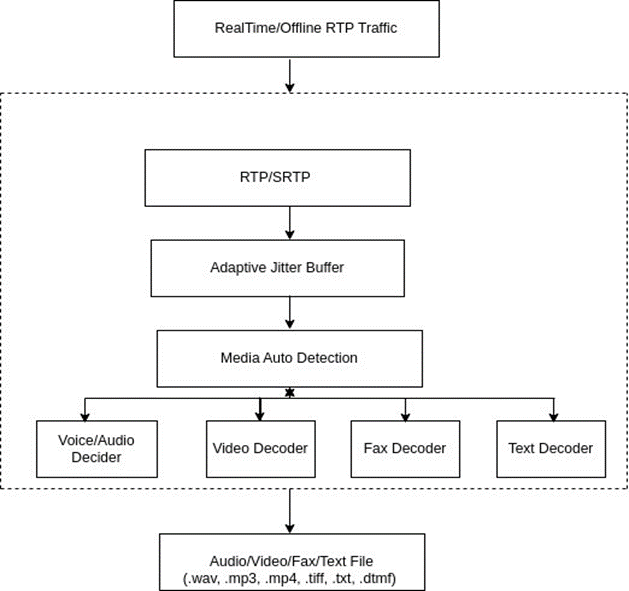
RTP traffic processing flowchart
3. Decrypting and Processing VoIP Audio & Video
- Legal decryption processes with decryption keys unlock encrypted SRTP streams.
- AI-powered forensic tools reconstruct VoIP conversations, detecting speech patterns, keywords, and sentiment analysis.
4. Advanced Voice Analytics and Speaker Identification
- AI-driven speaker recognition and phonetic analysis confirm identities in intercepted conversations.
- Automated speech-to-text conversion enables rapid search and analysis of intercepted calls.
Scalability of VoIP Lawful Interception Solutions
To efficiently intercept and analyze large-scale VoIP, VoLTE, and VoNR traffic, advanced interception solutions must be scalable. This involves:
- Cloud-Based Infrastructure: Leveraging cloud computing to handle large-scale VoIP traffic interception and storage.
- AI-Enhanced Processing: Utilizing machine learning for real-time VoIP decoding and analysis.
- High-Performance Computing (HPC): GPU-accelerated decoding ensures efficient media reconstruction.
- Distributed Network Monitoring: Deploying multiple monitoring nodes for comprehensive traffic coverage and reliability.
- Adaptive Interception Algorithms: Evolving machine learning models improve codec recognition, decryption, and speech analytics.
Compliance and Ethical Considerations
Lawful interception is subject to strict regulatory compliance under frameworks such as CALEA (U.S.), ETSI (Europe), and global privacy laws. Ethical considerations must ensure that monitoring systems are deployed only under legal jurisdiction, preventing misuse and safeguarding civil liberties.
Conclusion: The Future of VoIP Media Decoding
Decoding VoIP media for lawful interception is a critical capability for intelligence agencies, telecom providers, and cybersecurity firms. With growing VoLTE and VoNR adoption, interception solutions must integrate AI, cloud computing, and distributed architectures to keep pace with evolving network protocols. Advanced capabilities such as T.38 fax and RTT decoding, automatic RTP codec detection, and real-time/PCAP-based analysis enhance interception efficiency. Investing in cutting-edge VoIP decoding technology ensures lawful intelligence gathering while upholding security and compliance standards.
Get in Touch with
Consilient Technologies for robust VoIP decoding solution for lawful interception? Contact us at info@consilient-tech.com and visit the product page https://www.consilient-tech.com/voip-call-decoder today to learn how our advanced traffic analysis tools can enhance your interception capabilities and compliance adherence.

